



I am a Professor at the Department of Computer Science at the Rochester Institute of Technology, Rochester, NY.
You can find me in Room 3-521, Golisano Hall (Building 70), or you can contact me by means given here Please, see my schedule this semester.
Previously I worked at the Department of Computer Science, University of Texas at El Paso and School of Communications and Informatics at Victoria University, Melbourne, Australia.
Please, see my CV for more information and the publication list.

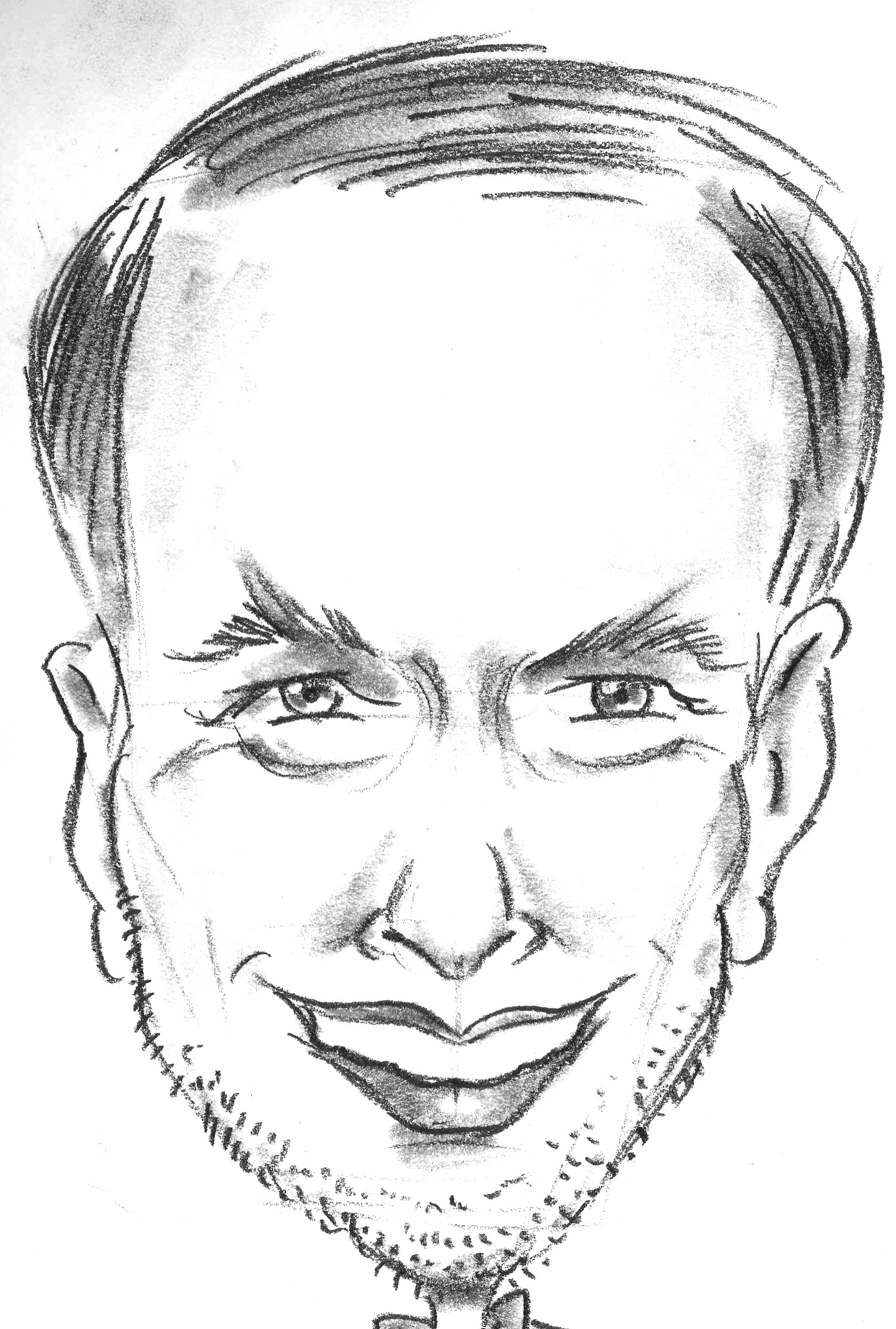
 Wiley and IEEE Press released my new textbook:
Leon Reznik Intelligent security systems: How artificial intelligence, machine learning and data science work for and against computer security. IEEE Press-Wiley&Sons, ISBN-13: 978-1119771531, ISBN-10: 1119771536, 2022
Wiley and IEEE Press released my new textbook:
Leon Reznik Intelligent security systems: How artificial intelligence, machine learning and data science work for and against computer security. IEEE Press-Wiley&Sons, ISBN-13: 978-1119771531, ISBN-10: 1119771536, 2022
Please, see more information
here. On this site, you can find my slides and lecture recordings for each chapter, also.
Please, contact the publisher if you want to buy the book or order the evaluation copy for your class.
You might like to look at the publisher book description or the flyer .
We are excited to work with our colleagues from Harvard University, Rochester Institute of Technology, Florida International University and University of Georgia on our research project funded by NSF Collaborative research: IDEAS lab: ETAUS: Smarter Microbial Observatories for Realtime ExperimentS (SMORES)
This big ($1.5M) project involves studies and practical work in biology, AI and engineering as well as field underwater experiments in Florida and California.
The project studies marine sediments, which play a critical role in natural carbon sequestration. We propose to develop a novel seafloor sensor/sampler array to better understand how tidal pumping and subsurface currents influence seafloor oxygenation and sedimentary carbon cycling.
Our group @RIT is responsible for developing smarter control systems that use machine-learning models and techniques to understand how to make intelligent predictions about when and where to best sense/sample based on the historical and real-time data. We plan to participate in the field work too.
Also, we are working on another collaborative international project IMPRESS-U: Exploratory Research in Robust Machine Learning for Object Detection and Classification (NSF award # 2415299) with the goal to design and implement a novel content-aware concept in data processing of multispectral images and object recognition by low-dimension CNNs, low-rank regularization, and information-dense eigenvector factorization on compact operator spaces.

Direction 1: Security and data quality evaluation, Big Data phenomenon: see my key address From Big Data to Quality Data: What is the emerging sensor and network technology going to deliver next? to NetWare 2014 , an umbrella event incorporating a few international conferences on November 20, 2014 in Lisbon, Portugal. Also, at the same conference I chaired the panel on November 19 on the topic Information Privacy: Does it really matter?
See our new paper Sergei Chuprov, Raman Zatsarenko, Leon Reznik, and Igor Khokhlov (2024) Data Quality Based Intelligent Instrument Selection with Security Integration. ACM Journal of Data and Information Quality, vol. 16, iss. 3, Article 15 (September 2024), 24 pages, https://doi.org/10.1145/3695770 was just published and designated as a research paper by ACM with an open access and free download.
Direction 2: Intelligent systems and sensor networks design, machine learning and neural networks techniques and their implementation, Big Data analysis: see a joint presentation with my former student Dmitri Yudanov Heterogeneous Implementation of Neural Network Algorithms to the AMD Developer Summit, San Jose, November 11-13, 2013
NEW Direction 3: that advances and integrates previous two to enhance learning AND security and privacy protection with the following directions: Advanced and Secure Federated Learning, Knowledge and Metacognition Integrated into Networked Learning Systems.
Here we investigate novel techniques integrating metacognitive features for distributed learning optimization, privacy protection and security enhancement: please, see my invited talk at the Workshop on Metacognitive Prediction of AI Behavior, November 13-15, 2023 at Arizona State University, Scottsdale, AZ titled mLINK: Machine Learning Integration with Network and Knowledge or An Attempt to Look at Metacognitive Prediction From a User Practice and to Offer Some Possible Solutions from our own experience and my latest publications.
I recommend our paper:
Zatsarenko, R., Chuprov, S., Korobeinikov, D., & Reznik, L. (2024). Trust-Based Anomaly Detection in Federated Edge Learning,
doi: 10.1109/AIIoT61789.2024.10578967 , for which my student Raman Zatsarenko won the BEST PRESENTER award at the 2024 5th Annual IEEE World AI IoT Congress (AIIoT), Seattle, WA, USA, 29-31th May 2024,
and other new publications:
D. Korobeinikov, R. Zatsarenko, S. Chuprov, A. Barea and L. Reznik, "IntelFL Framework: Optimizing Federated Learning with Metacognition for Application Design and Deployment," in IEEE Intelligent Systems Journal, 2026, doi: 10.1109/MIS.2026.3658072.
S. Chuprov, L. Reznik and R. Zatsarenko, "KISS: Knowledge Integration System Service for ML End Attacks Detection and Classification," in IEEE Transactions on Dependable and Secure Computing, vol. 22, no. 5, pp. 4783-4794, Sept.-Oct. 2025, doi: 10.1109/TDSC.2025.3553807
Zatsarenko R., Chuprov S., Korobeinikov D., Reznik L. & Pena A. (2026) “How to Improve Federated Learning in Consumer Applications? Detect and Exclude Bad Clients” in 2026 IEEE 23rd Consumer Communications & Networking Conference (CCNC). 2026. doi: 10.1109/CCNC65079.2026.11366313.
R. Zatsarenko, S. Chuprov, D. Korobeinikov, L.Reznik, A.Pefa MADE-PI: Framework for Effective Anomaly Detection in Federated Learning Applications, 24th IEEE International Conference on Machine Learning and Applications, Boca Raton, FL, December 3-5, 2025, pp.446-451, doi: 10.1109/ICMLA66185.2025.00067
Please, see
our publications and mobile applications
for more information about our Data Quality and Security Evaluation framework and its implementations on mobile devices.
Want to learn even more?? Please, look at my current research activities, my latest publications and other information . If you are interested in collaboration, please, contact me .
 Want to meet in person? Our group will be presenting our research papers at the following conferences:
Want to meet in person? Our group will be presenting our research papers at the following conferences:
Main directions for possible student projects are presented here (note, this presentation introduces directions only; I am happy to discuss with you how they could be adjusted to your interests if you might be interested in my supervision)
Courses taught previously:
Courses taught before at other schools:
Copyright � 1997, 2005, 2008, 2012, 2015, 2018, 2022, 2023 Leon Reznik